Cybercrime is one alarming activity in the world of the Internet, and as such, every individual, business, and Parastatals is fighting hard against this menace. And this leads us to the topic of today – The honeypot Trap.
Honeypot Trap is a method used to lure hackers into your system. It is like a ‘know your enemy’ decoys initiated, looking exactly like the product or services you want to trap by manipulating them into a click-bait and, with so doing, revealing themselves knowingly.

This has become something important, like a must-designed program due to the increased rate of cyber crimes resulting in several companies' lapses, hence the prompt need for cybersecurity like Honeypot Trap. Online space has always been viewed as malicious space even though there are advantages to be noted; if you cannot secure your privacy and security, then you are ten steps out and one step in, and this can be frustrating.
However, in every online atmosphere, it would be better to have a built-in team of cybersecurity experts to handle and pilot all the affairs regarding online activity to prevent malicious actors from carrying out their evil acts. Baiting cyber attackers to their own built game seems interesting so long as hackers haven't slotted in already before setting up your decoy shield.
One thing to note is that there are several Honeypot traps for every program your organization is made of, and one has to be alert as you might be observing one while hackers have invaded others of their interest, hence the need for cybersecurity tools. In this article, we will take you through everything you need to know about Honeypot traps.
What is Honeypot Trap?
Honeypot Trap is a cybersecurity program that is falsely designed as a decoy to manipulate and trick cyber-attackets into revealing themselves. It helps spot unauthorized access to a system. This is often configured to mimic functionalities to look exactly how the production system stands out for looks like.
It is reliably designed to fine-tune and redirect cybercriminals from legitimate production systems. And also to a specific location you want them to be in order to quietly take a backseat to observe behind the scene what the attackers are up to, how they operate, their strategies used, and their purpose in entirety.
Just as its name implies, the Honeypot trap set in honey that is hard not to compromise with. It is a click-bait that work accordingly, play the hackers' games, spot new attacks, and as well spot attackers' identity. With a Honeypot, trap comes several points and needs of configuration either on a software service or even on a network at large.
Also, with it being deliberately designed toward a targeted interest, oftentimes, it uplifts and enhances production systems and organizations' cybersecurity team and their threat awareness level. However, with the Honeypot trap set in place, perfectly and purposefully, future cyber attacks measure can easily be understood and taken into cognizance.
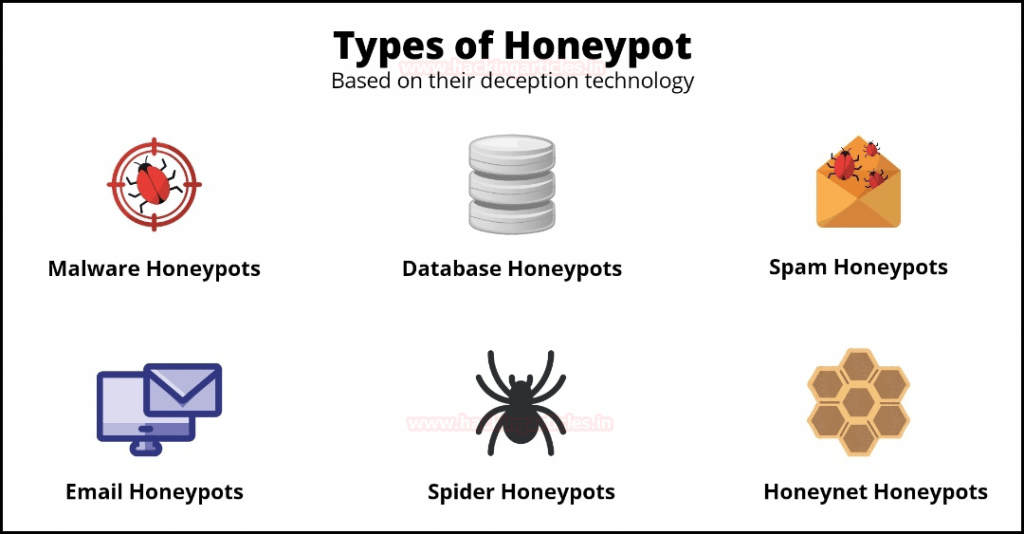
Types of Honeypot Trap
Basically, there are several types of Honeypots, all working in accordance with their strength and threat handling level. Most times, Honeypots are classified based on the level of interaction complexity, purpose, and even activities. Below are the most known types of the Honeypot trap.
-
Low-Interaction Honeypot
This type of Honeypot has low complexity compared to the other types we will be discussing in this article. The low-Interaction Honeypot model is exactly what hackers are looking for since it has a short feedback time. They often catch limited interaction and information because their resources are considerably low, and this can result in this type of Honeypot not being able to completely lure attackers into revealing their full details because of low-level decoys.
Since their functionalities are low, most times, the major attacks they spot are the locations of the attackers. One top Honeypot in the low-interaction category is Honeyd. Commonly used for a production system.
-
High-Interaction Honeypot
This type is the opposite of the low-level interaction type. They run on a highly sophisticated production system. This type has complete and certain click-baits that will sure get cyber attackers where they will be encountered as being malicious, hence, revealing their identity by themselves unknown to them.
With the high level of interaction possessed by this Honeypot type, system vulnerabilities can easily be spotted as the cybersecurity team can as well take a backseat, relax quietly and observe how cybercriminals go about their place of interest in the system, the tactics, and which log files are mostly their source of the hack, and they find interesting.
Multiple activities are hosted to keep hackers on the network longer. They are highly secured compared to low-interaction Honeypot. Cyber attackers cannot detect they are being lured. This type of Honeypot is mostly used by organizations, researchers, and government parastatals. They are very expensive to maintain but highly effective.
-
Pure Honeypot
This is a type of Honeypot that uses bug taps to monitor the activities of the attackers intensively. In this type of Honeypot, no software is involved. The bug traps are installed to the Honeypot link of the network, hence easy monitoring of attackers' points of interest.
They are not as effective as the high-interaction Honeypot. They are fully-blown or fully-fledged production systems. Using this type of Honeypot, data are made to be confidential and vulnerable in order to track attackers' activities.
Pros and Cons of Honeypot Trap
The honeypot trap is supposed to be an integral part of every organization's cyber security list of tools. Since its part of cyber security strategy help to easily detect the intentions of hackers trying to invade your system privacy. Below are some of the pros and cons that define why the Honeypot trap shouldn't be an option for production or an organization's cyber security activities but rather a core point.
Pros
- They can ensure visibility of both internal and external security.
- Once installed and configured into the production or organizational server or network; hence all tactics and log files of interest can be known.
- Since Honeypot help reveals attackers' interest point, production and organization systems could easily take precaution and enhance better cybersecurity team
- With the Honeypots trap network or server, activities can be fine-tuned in a Know your enemy stand, and it will look exactly like the original in order to redirect hackers from having eyes on legitimate system zone.
- Leveraging Honeypot can help spot the exact location of attackers and the exact digits of dangers they are likely to cause by intruding.
Cons
- One con of Honeypot is that, by types, some are interaction base, and using such to try and spot attackers can lash back if attackers are using more advanced production mechanisms, and instead of spotting hackers, you do rather be spotted.
- Some attackers could be experts in what they do by launching false attacking alarms to distract companies from their area of focus.
- Sometimes, not choosing the type of Honeypot you use can trigger risk instead of preventing it. A compromised Honeypot trap will sure cause issues big time on the real server or network.
- The honeypot trap should not be the only cyber attacker or detectable tool used in a network; else, over usage can result in less productivity and effectiveness.
How does Honeypot Trap Work?

Mind you, Honeypot is not meant for protection majorly, it's sole aim most times is to spy and spot hackers and unauthorized users. With Honeypot traps, a system is falsely striped-off major confidentiality to make them seem and appear 90% vulnerable to cyber attackers. This is done so that there is no way the hackers or attackers can spot any red-flagged or foul place to lure them into revealing themselves.
Honeypot being a decoy or trap is configured to mimic the exact ways of the production or research system it stands for. They create several unique and viable hints for hackers to get spotted and lured to where they will encounter the eyes of cybersecurity observers quietly looking at the hackers and monitoring their invading techniques used, files of interest, and many more in order to enhance their intuition security system.
There are several ways to lure an attacker confidently and make sure their malicious activities to seem true to them. Among many is to design a Honeypot trap to make internal port opening seem vulnerable to a port scan which will further interest attackers to invade the opening ports and try to steal or hijack information.
Another is designing a Honeypot trap of credit cards. This is a top-notch technique to spy on attackers and lure them to where you want but with all this having a very strong Honeypot tool that can never fall victim to attackers' tricks is something integral.
It is obvious everyone loves anything that has to do with generating revenue, but attackers do not want to know if it's legit or not; all they want is what they want, and that's the credit card details for customers' billings. However, designing a system that seems pretty an opportunity to satisfy their desire in that aspect and at the same time technical to match up their game will sure ride smoothly.`
Also, one other strategy that works well is designing a Honeypot trap that tends to appear to be compromising your production or organization system, intellectual property, trademark secret and etc., therefore tricking the attackers with the link of franchise access without any record of infringement.
However, this will help cyber security preparedness for future activities. But these Honeypot designs and configurations must not be obvious, like no second thought from the attackers, but rather very attractive, interesting and appear 90% legitimate as that's the only trigger to lure attackers in and stay longer to take other steps.
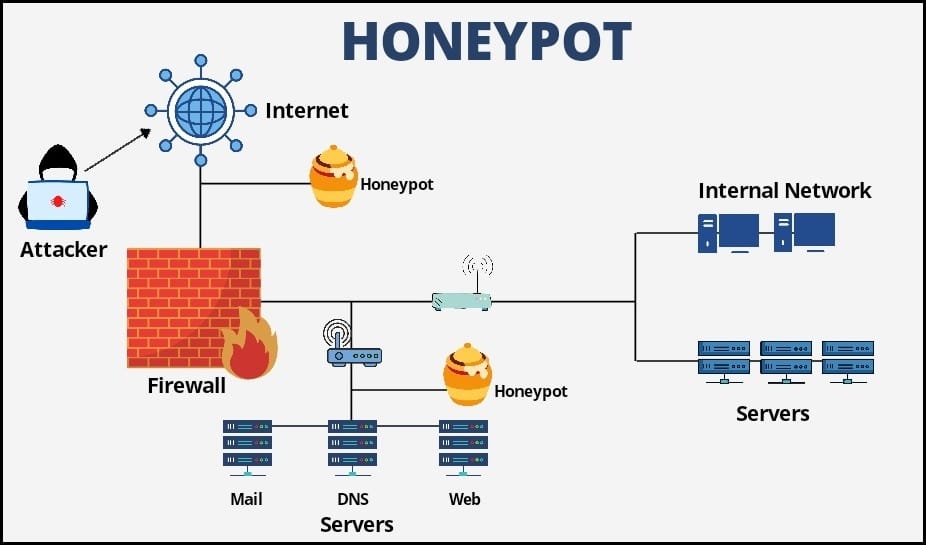
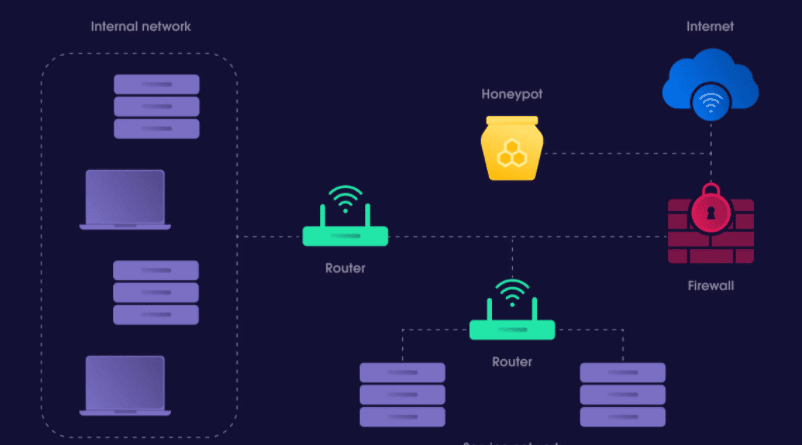
Honeypot Vs. Honeynet
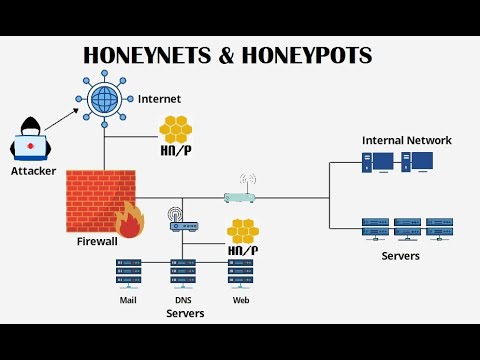
These two networking traps seem to be the same and are being used interchangeably. Although they seem similar in functionalities, they are not the same. A honeynet is the network of several Honeypots. It is hosted on multiple systems like Windows Honeypot, Mac Honeypot machine, and Linux Honeypot machine. Honeynet has servers, networking devices, and systems that are similar to a legitimate network having false data.
Honeynet has it internal and external firewall. Using Honeynet might as well make you appear more vulnerable but when it comes to having a Honeynet on your internal network is risky unless attackers are trapped within it. Since it's a network of several Honeynet, it does almost all that Honeypot can do.
While Honeynet deals with several Honeypots, and they seem similar. There are differences. A honeypot is a decoy or trap that tricks and lures attackers to where they would be encountered and observed to know the interest and functionality of the attackers. Over 70% of security incidents occur due to insider threats, i.e., internal.
Installing a Honeypot with proper configuration in order to be able to monitor attackers' movement on your internal network will help create privacy within your internal intel. Honeypot can spot misconfiguration. It is useful for alarming any exploit. Having Honeypot installed and configured will sure help foster cybersecurity.
Complexity of Honeypot
Honeypot comes in categories and is a tool that lures attackers to a needed zone. The complexity of Honeypot is also deep into the several types in accordance with the activities they perform and carry out. Below are some of these activities.
-
Decoy Honeypots
This is a type of Honeypot that is being set up to trap and monitor the vulnerability of software deliberately. Decoy Honeypot databases such as SQL injections are pretty known. Their databases are used to gather data about the attackers and therefore distract them from the legitimate databases on their database server.
-
Spider Honeypot
This is designed with the purpose of trapping web crawlers and scrapers by creating web pages and links solely for crawlers. This type of Honeypot can foster an organization's awareness of bot activities and how to block their malicious techniques.
You may be like to read,
- Captcha avoidance 101: How to Avoid Captcha More efficiently?
- How to Scrape a Website and Never Get Blacklisted & Blocked
-
Email Honeypot
This type of Honeypot uses inactive email that has not been used for so long to spot and reveal spammers. The strategy here is to design a false Honeypot trap to place a false email address in a hidden location in the mail where only an automated address tool for spotting spamming bills will be able to find it. The address used has not been on anything other than the spam, then if in the scenario or settings, it is confirmed that any email entering their inbox is spam, it will be alarmed out; hence the organization can block all spam emails received.
-
Malware Honeypot
These types of Honeypots are designed with the sole aim of getting anti-malware software as an end result. But before that, software apps and APIs are created to mimic exactly the malware attackers already seem to lure in malware.
-
Client Honeypot
These types of Honeypot are designed to lure in malicious server attackers to use in attacking clients. They appear as a client and quietly observe how attackers make malicious differences to a server while attacking. These Honeypots run in a virtualized space.
Production Vs. Research Honeypot
Honeypots by classifications are of several categories of which production and research are Honeypots of purpose.
-
Production Honeypot
This is a common type of Honeypot. Majorly used by businesses and organizations. Production Honeypots are not as complex and sophisticated as compared to research Honeypots. The aim of this type of Honeypot is to spot active attackers on the internet network of businesses and organizations using it as a distraction by redirecting hackers away from legitimate systems.
-
Research Honeypot
These types of Honeypots are complex and sophisticated in comparison with production Honeypots. They are designed and used by researchers to better get the gist of attackers or hackers' codes, tactics, what keeps them invading further, files of interest, and system vulnerabilities. They are majorly used by government parastatals, intelligence, and research organization. This will help the bodies involved to be both security aware and cybercriminals invasion tactics.
Risk of Honeypot

Below are some risks associated with Honeypot.
- Honeypot is not protection security for systems; they are designed to get cyber attackers to spot cyber attackers and threat invasion; therefore, relying solely on it will do no good as it will only play the role it's installed for.
- It can be gradually risky if attackers have already invaded a production system before a Honeypot is designed for it, as the hackers will misinform the Honeypot and move to the other part of the system.
- Honeypot will only play its part as a decoy to deceive the attackers and redirect them from the legitimate networks. It cannot always spot multiple hackers if it's not configured for that particular program in the production or research system.
However, it is recommended that while you use Honeypot, you should also support it with other cybersecurity tools as Honeypot cannot serve all cybersecurity purposes.
FAQs About Honeypot Trap
Q. Does Honeypot Actually Work?
When done and used correctly, honeypot works. It is actually a good way to find out the activities of hackers and other people with malicious intent. It is also used for exposing vulnerabilities in a system. One example for a honeypot can show the high level of threat posed by attacks on IoT devices. With a honeypot, you can study and block threats. However , you need to know that honeypots are usually meant for specific threats and not even meant for stopping threats on their own.
Q. Can Honeypots be Hacked?
Honeypots are a great way to lure hackers into a system to reveal their activities. From the above, you can tell that honeypots works. But can it be hacked? Once a hacker knows there is a honeypot setup, then he can hack it or give you fake signal to make you make the wrong decision. It might interest you to know that hackers are even on the lookout for honeypots to distract before carrying out their malicious acts.
Conclusion
Honeypot has been seen to be a cybersecurity tool that is used to trap and decoy malicious attackers falsely. There are different types of them ranging from one category to another, hence, defining their strength in terms of interaction levels.
Engaging your production system in Honeypot activities requires a particular one that is compatible to carry out the trap you want to set forth so that it should not back-lash and instead of luring and controlling a hacker it becomes otherwise used due to low production mechanism level. This article comprises a well-researched write-up that keeps you informed on Honeypot Trap.
Learn Some hacking tricks to protect yourself online,