Breaking into someone’s computer system requires a certain level of technical expertise. However, hacking into people’s computers for personal gains or to cause damage is considered illegal.

You could practice white hat hacking instead, so you do not have to worry about getting fined or even sent to prison. White hacking involves hacking your own system to know it works or something.
Do you want to gain access to your friend’s computer regardless, but do not go know to go about it? Well, by the time you are done studying this article, you would have already known how to do that, using their IP address by getting one-time access to their computer when they are not around. In this article, we would be showing you how to hack into someone’s computer using their IP address.
How do IP Addresses Work?

All devices communicate amongst themselves by sending, and receiving information using IP address. IP addresses make it possible for devices to communicate remotely. The IP helps your device connect to the Internet by passing through a network called ISP (Internet Service Provider).
More like a link through which your phone accesses the Internet. Your ISP provides you with a device called a router, which helps your devices connect to the Internet or just interact with one another.
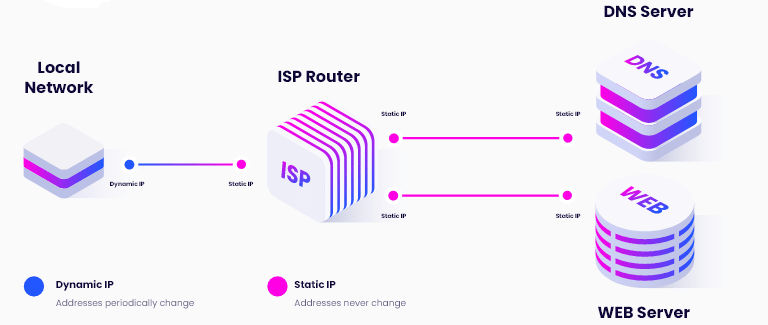
IP addresses are assigned by the ISP and in the current world of mobile devices, IPs change more frequently than you think. Simply put, IPs are dynamically assigned by ISPs and as such, most devices do not retain the same IP address for a long time.
However, some ISPs do provide static IPs depending on a lot of factors. Even for the static IPs, a switch to a different provider will mean a change of IP address for your device. So, think of IP as an agent that makes it possible for you to access the internet anytime you want. One whom your internet or non-internet activities are communicated through, all behind the scenes.
Read more, How Are IP Addresses Assigned?
How to See Your Computer's IP Address
1. Using CMD
Whether you know your IP address or not, it does not really make any difference unless you want to be able to control the network remotely or perform in-network troubleshooting.
There are many ways you can use to know your IP address. However, the command prompt method is one of the easiest and most reliable methods. Below is how to use the command prompt to get your IP address.
Step 1: Press the Start button
Step 2: Type “cmd” into the search box at the bottom of this window
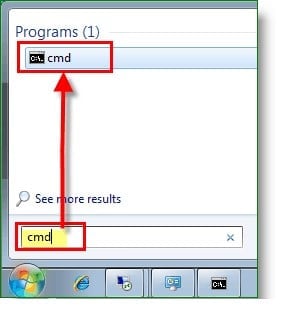
Step 3: Tap Enter when the Command Prompt comes up
Step 4: Type “ipconfig” on the screen and press Enter
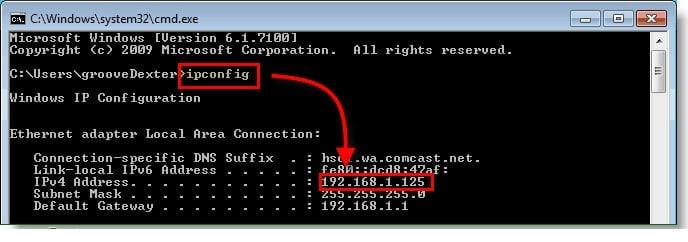
Step 5: Look for IPv4 and trace that line towards the right-hand side to see your IP address.
2. IP address Checker Online
| IP Address: | 207.46.13.107 |
| Your ISP: | Microsoft Corporation |
| Organization: | Microsoft Azure Cloud (westus2) |
| ASN: | AS8075 Microsoft Corporation |
| Country: | United States, US |
| Your Region: | WA |
| Your City: | Quincy |
| Postal Code: | 98848 |
| Latitude & Longitude: | 47.233, -119.852 |
| Time Zone: | America/Los_Angeles |
How to Get Someone's IP Address Using Grabify
Step-by-Steps Guide to using Grabify
The method described above will only work if you have physical access to the person’s computer. If the computer is out of your reach such as in the case of people you meet online. For accessing the IP address of someone remotely, you will need to use an IP Grabber such as the Grabify tool.
This tool masquerades as a URL shortener but in reality, it is an IP logger that can get the IP address of users that visits shortened URLs it creates. Below is a step-by-step guide on how to make use of it.
Step 1: Visit Grabify

Step 2: On the empty field provided, enter any URL of your choice, preferably, one that looks very genuine and will not raise eyebrows. You can refer to the image for a better understanding.
Step 3: Next thing is to click on the Create URL

Step 4: An agreement page will pop up. Click on the I Agree & Create URL
Step 5: Now it opens up your dashboard where you can see the functions. Here, the details of whoever you will be sending your new link to will be revealed including their IP address, which is why we are doing this in the first place. Note that the link you are sending to your victim could be a Facebook profile link, a LinkedIn link, or anything to trick your target into clicking.
Step 6: Now slide the Smart Logger toggle on to get more details of your target than you would ordinarily get without the Smart Logger feature. Refer to the image below.
Step 7: Now send the URL you have just created to your target. As soon as they click on it, their IP address, as well as other details, are revealed to you. This, however, is dependent on how genuine your link looks for them to click.

Step 8: Note that the 0 result on the image above changes to 1 when they click your link. Let’s see a confirmation below:
Step 9: Now, below the Results—, which have changed to 1 due to the recent click by your target—you will find a clustered detail about your target, click the long details to reveal his details more clearly.
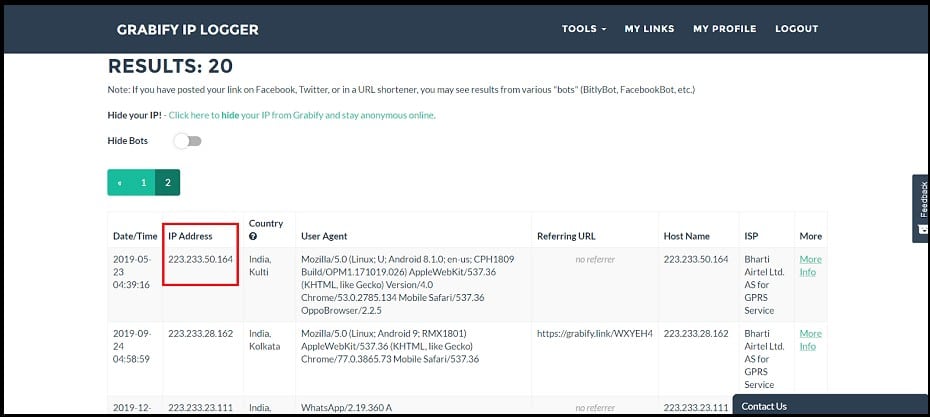
Step 10: The details covered in red ink are your target’s IP address but to see other information, click the highlighted area. As soon as you click this information, the one below comes up.
Again, your target’s IP address is one covered in red ink in this case. On your own, it will be revealed, it’s only this for example purposes. As seen in the image above, with Grabify, you can also know the location that your target is currently in.
Other information such as country, date/time, language, timezone, and browser information is not left out. Now that you have your target’s IP address, you can refer to the steps below.
Read more, How to Find out Someone’s IP Address?
How to Hack Someone's Computer with Their IP

Now let's head on to the nitty-gritty of this article, in this part, we shall be discussing the step-by-step method of hacking Someone's computer using their IP address. This method of hacking can help you hack someone's computer remotely. In other words, after the first
Step 1: Use the above step to open Command Prompt.
Step 2: Type in “net use” command. This command is another Network Basic Input/Output System (NetBIOS) that shows you how to hack remote drives or printers.
Step 3: When done successfully, you will get a feedback message like this: “The Command completed successfully”. Well, at this point, your mission of hacking your target's computer is almost accomplished.
Step 4: Now go to My Computer on the computer and you will find a new drive amongst the existing ones named Shared. You access your victim's files by opening the drive. You can copy photos, folders, or offer files into your own computer, but first, you should enable Write Access on your target's system to be able to do those. Anytime you want to gain access to your target's system, you can do that through the Command Prompt.

The IP address method is obviously a bit complex and therefore requires you to have a high level of technical expertise to be able to successfully carry out your hack.
How to Prevent IP Hack
Well, in order not to make you a soft target there are certain measures you need to put in place. Hackers love to take advantage of careless users and hack their computers thereby causing them mayhem, which you sure do not want to contend with.
-
Use a Strong Password

You might be wondering what problem a strong password will solve here or which of your device it concerns. Well, all your device should have a strong password in order to keep them secured since any hacker has to have access to your device first before they can carry out any hack whatsoever.
A strong password is one with both upper and lower case alphabets, numerals, and characters. Ensure that your devices are locked with these elements of a strong password, and you would not have to worry about any penetration by anyone.
-
Use VPN

VPNs make it very difficult or even impossible for your device's IP address to be accessed. This is because it masks your real IP address from being detected by tools such as Grabify.
It is because of this that Internet security experts advise Internet users to use VPNs for their day-to-day Internet use. Proxies are a good alternative to VPN services but they are not as secure as proxies because of the encryption done by VPN that proxies do not.
- How to Get a Fake IP Address to protect your privacy
-
Do Not Click Every Link
You may have received emails with suspicious links in the past urging you to click the link in order to achieve something. Clicking such links puts you at a very great risk of revealing your computer IP address and also exposing you to other security and privacy risk. So you are better off ignoring whatever link is pushed to you, or at worst, scrutinizing it properly to be sure it's not harmful.
Conclusion
Hacking someone’s computer is like getting access to their personal affairs through the back door. Many hackers are waiting for you to become careless with your devices so they could take advantage. Please make sure all access is blocked to prevent, or at worst, minimize hack.
And if you are the hacker in this case, please bear in mind that getting access to and information from people's computers by forcing your way into their data without their interest or approval is considered criminal. If you must hack into someone's computer, please have a good reason for doing so, and educate yourself on the possible consequences that there may be.