Tons of proxies online, Http(s) proxies, socks4/5 proxies, dedicated Proxies, shared proxies, open proxies, Anonymous Proxies, elite proxies, Reverse proxies…Is it confusing? Read this post to comprehend all of that.
The proxy can be considered as a middleman between you and the web server (Terminal Server) where your desired website is hosted. It receives your request and then sends the request to the web server. The web server then processes the request and sends back the requested information to the proxy server which then finally sends the requested data back to you.

This is similar to you seeking your friend to ask another person a question and then let you know the answer. A myriad of proxy servers has been invented for different purposes using this simple concept. These can easily confuse you if you are new to learn about proxies. Let's discuss these different types and their uses in this article.
Proxies can be divided into several types based on different criteria. For our discussion, we will talk about different kinds of proxies based on protocol, anonymity, usage method, request modification, sharing, server type and so on.
Different types of proxies due to the protocol
HTTP Proxy Vs. HTTPS Proxy Vs. SOCKS proxy
Based on the protocol the proxy server uses, there can be HTTP, HTTPS, SOCKS proxies.
HTTP Proxy
An HTTP proxy is any proxy server that uses Hyper Text Transfer Protocol (HTTP) to connect to the web server or the client (browser). Due to the widespread use of HTTP on the internet, the majority of the proxies are HTTP proxies.

These proxies can access the web pages that you browse on the internet. Although they can also access websites using Secured HTTP (HTTPS), the cost is losing the original SSL Certificate in the process.
Since HTTP connection can interpret data easier than the SOCKS protocol, bots and scrapers perform better with HTTP proxies.
HTTPS Proxy & SSL Proxy

SSL (HTTPS) Proxy: SSL or Secure Socket Layer is an additional layer of security imposed on the HTTP to make it HTTPS. This layer adds security certificates that are used for end-to-end encryption to prevent eavesdropping during data transmission.
A proxy server equipped with SSL establishes a secured connection to the client and also to the webserver to avoid any outside intervention. HTTPS Proxies helps you stay safe while making transactions or logging into websites using username and password.
SOCKS Proxy
SOCKS Proxies creates a TCP connection on behalf of the client to route traffic. This is a method of tunneling through firewalls, and even the proxy server cannot intercept the data, so the socks proxy support much more application. This way, a SOCKS proxy is much more secure than HTTP proxies.
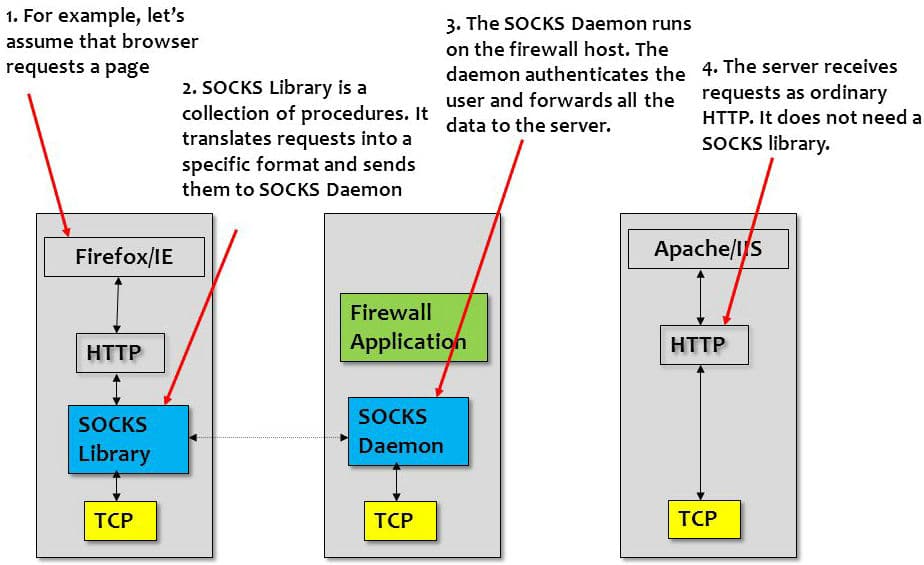
However, SOCKS5 proxies add even more advanced security features to make the connection safe. The only downside is, some bots don’t support SOCKS proxies, and so you’ll need to make sure if your bots support SOCKS proxies.
Different types of proxies based on anonymity level
Transparent Proxy Vs. Anonymous Proxy Vs. Elite Anonymous Proxy
Transparent Proxy
Transparent proxies are also termed as intercepting proxy, inline proxy, or forced proxy. These proxies do not modify the requested or responded data, so there is no anonymity involved, and websites can read your IP address. Transparent proxies are usually found in public wifi hotspots to grant access to only those with permission. Many servers also use transparent proxies to cache content for fast delivery.
Anonymous Proxy
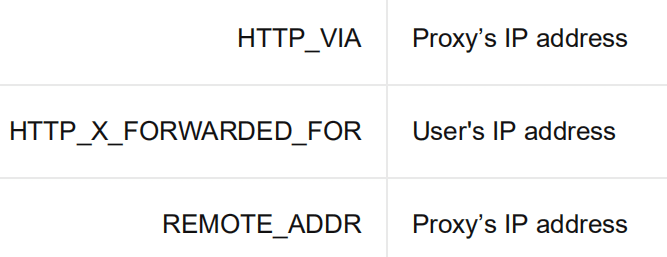
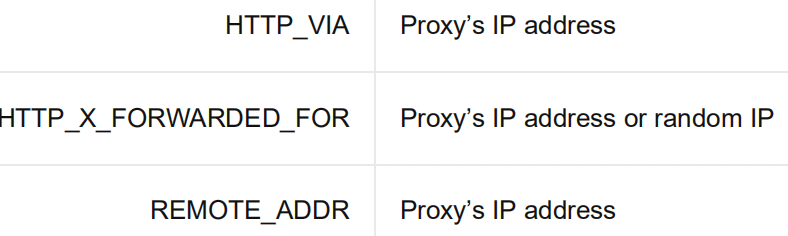
Anonymous proxies modify the HTTP header to replace your IP address with their IP and add additional forwarding commands to prevent the web server from knowing your IP address. The websites can recognize that a proxy server is bypassing the connections but cannot tell your initial IP address. These types of proxies provide bare minimum anonymity and can be of any protocol.
Elite Anonymous Proxy
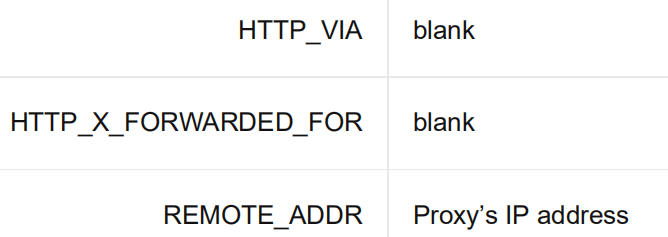
Elite anonymous proxies are similar to anonymous proxies, but it is much safer since they offer the highest level of anonymity in a proxy. The proxy server modifies the HTTP header to completely remove any of your information and does not add any forwarding commands. This way, the website does not recognize the connection request to be from a proxy server and treats it as any general connection.
Elite anonymous proxies are essential if you use sneaker or scraping bots to prevent the webservers from knowing that you are using proxies and getting your IP banned.
Types of proxies based on IP origin
Based on where the proxy comes from, it can be either datacenter proxy or residential proxy.

Datacenter Proxy
These proxies are generated in servers dedicated to handling proxies. The servers are specially configured with high bandwidth connections and specialized software to maximize performance. These result in proxies that have fast speed, lower ping and can have elite anonymity. Datacenter proxies are suitable for most of the business purposes, especially for bots.
However, since this requires the seller to have a data-center in each of the locations from where they want to offer IP addresses, often the location diversity is much less for datacenter proxies. The total number of proxies a seller owns is also limited and in the vicinity of a few thousand. Hence, ticketing or sneakers proxies can be easily found you now use datacenter proxies, so It's much easy to block with the similar subnet.
Residential Proxy
Residential proxies are IP addresses that are used by real people in their homes and provided by real ISPs. The seller of residential proxies does not own the proxies, but merely ‘rents’ them in exchange of services such as residential VPN.
This lets the sellers have a massive pool of residential proxies from practically all over the world. These proxies are comparatively slower than datacenter proxies but are suitable for many businesses uses due to their extensive collection of proxies, Learn more about what's the residential IP proxy Here.
Different types of proxies based on usage method
Open Proxy Vs. Closed proxy Vs. Web Proxy Vs. CGI Web Proxy
Open Proxy
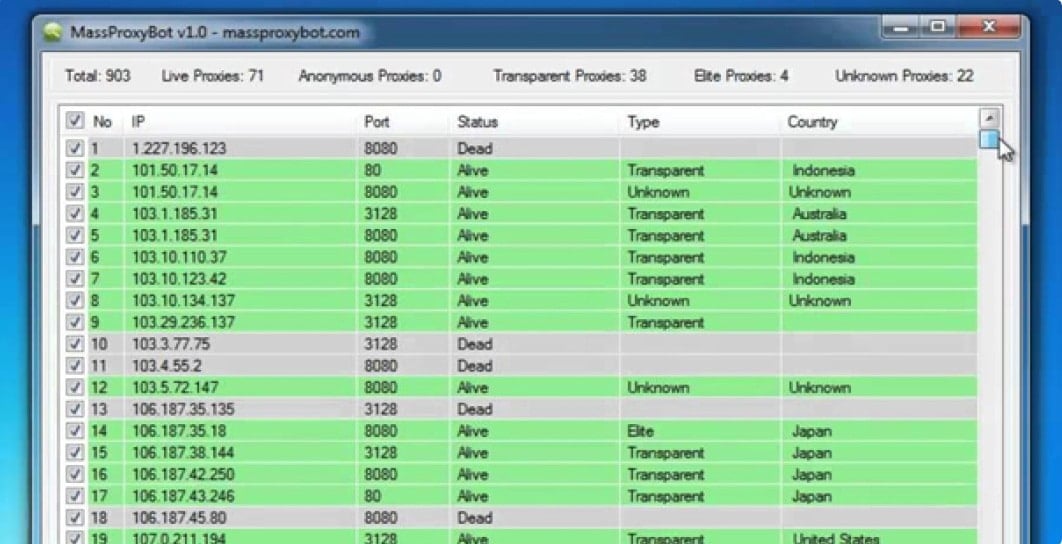
Open proxies are publicly available proxies that do not require any authentication method while configuring. But as these are free and publicly available, most of the time these proxies are dead or not secure since they can be set up by hackers to steal information.
The open proxies are also known as the public proxies, so it's almost free fo charge, And we do not recommend you use those free public proxies, the reason is here.
Closed Proxy (Private Proxy)
Closed proxies are proxies that are protected using different authentication techniques to prevent any unauthorized use by people without access. Closed proxies can be purchased from numerous vendors online. Closed proxies can be of two types based on the number of people the proxies are shared between.
-
Dedicated Proxy
Dedicated proxies are also known as private proxies since these proxies are allotted only to you, so access to the proxies is private to you. Private proxies offer higher performance and security but cost somewhat more than the shared proxies. Proxy packages that are specialized for ticketing, scraping, sneakers coping are almost always private proxies since they require heavy-duty performance and having the proxies shared by others increases the chance of getting banned.
-
Shared Proxy
These proxies are shared among 2-5 users. Each user can have a concurrent connection to the same IP at the same time, so the bandwidth usage is divided equally between the users. The downside of using shared proxies is that they offer significantly slow bandwidth speed due to the sharing and the proxies can get banned due to other users. However, shared proxies are generally provided at a much low cost than private proxies, Learn why Here.
-
Private Rotating proxy
Those types of proxies, also kind of closed proxies, for It's only shared with few users to use. 90% rotating proxy providers shared their proxy network to their users, Through scientific and rational allocation, keep fast speed network, some providers also offer exclusive rotating proxies also, mean only one user uses the proxy at one time.
Web Proxy Server
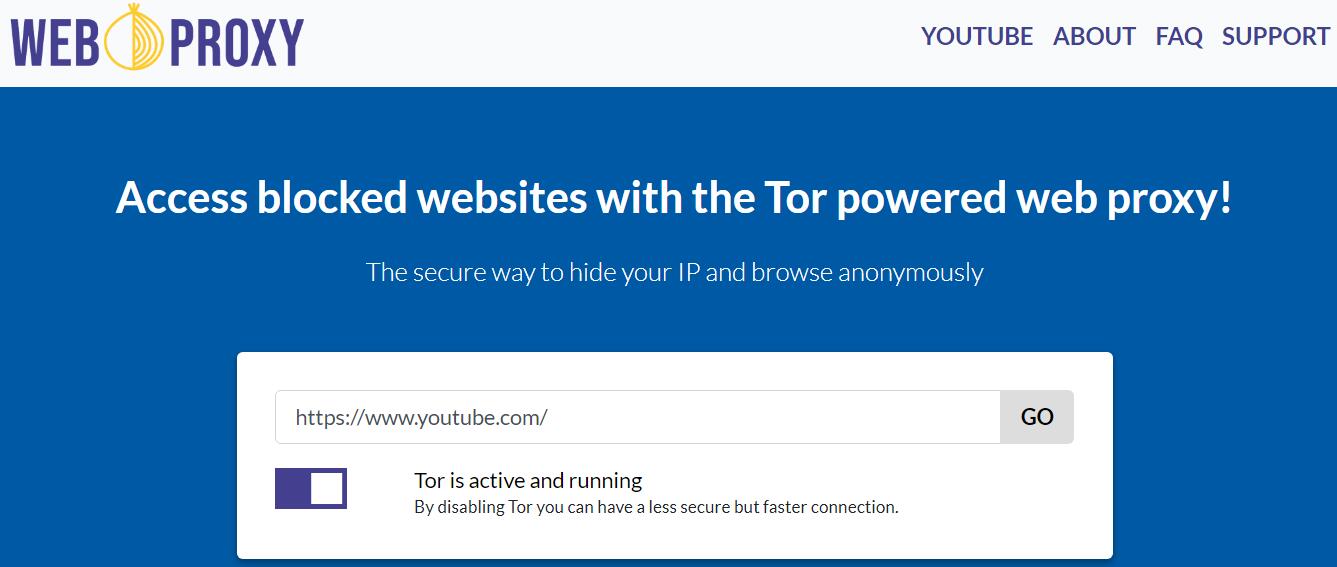
Web proxy means step a proxy server on a website. These are web proxies that no need configured on your desired application such as browsers or bots to use the applications normally. This type of proxies is just like a website you can mask your IP address.
- CGI Web Proxy
These proxies are run by web interface called Common Gateway Interface on websites. You can enter your desired URL to visit the page from the proxy website itself. There’s only a handful of CGI Web Proxies that are used by thousands of web proxy websites.
All data you enter while using these proxies are bypassed through the host website, and they can easily read your data if they want to. So, no secure information should be entered in these proxies. These proxies also cannot be configured to configure in software, making them unsuitable for most business tasks.
Types of proxies based on the proxy duration
Static IP proxy Vs. Rotating IP proxy
Non-rotating or static IP Proxy

Most of the datacenter proxy providers allot a certain number of proxies to a user for a price and the price increases for packages with more proxies. These proxies are allocated only to the particular user, and the user can use the proxies in a rotating fashion using bots or plug-ins.
If the proxies get banned, the sellers usually offer replacement of the proxies once per month. Apart from this, the user is stuck with the proxies.
Rotating or back-connect Proxy

Backconnect proxies are also known as rotating proxies since the proxies change automatically after a particular time and get replaced by new ones. This allows you to make each request with a new IP address and have much better anonymity, speed and avoid limitations in the bots.
Backconnect proxies are perfect for scraping. Backconnect proxies are mostly found in residential proxies due to the vast number of proxies to rotate from, but some datacenter proxy providers are experimenting with rotating datacenter proxies.
- Read more to know how rotating backconnect proxy works Here.
Types of proxies based on the modification of data
Forward proxy Vs. Reverse proxy
Forward proxy
A forward proxy is the general proxies that you use when accessing web content anonymously. This type of proxies is used by clients (browsers) to stay anonymous. Forward proxies take the data request from the client and then forwards the request to the web server to process and again forwards the response from the web server to the client. In effect, all of the proxy types we have discussed above are forward proxies.
Reverse proxy
A reverse proxy usually resides in the web server side to control traffic to the server, authenticate or decrypt connection requests or simply caching content for faster delivery. Reverse proxies are not used by general people for gaining anonymity. Instead, it helps a web server to stay protected from attacks. Reverse proxies can also distribute the traffic to different servers to balance the load.
Types of proxies based on IP reusing
Unused or Virgin Proxy
Proxies that have not previously been used are termed as virgin proxies or unused proxies. Most often than not, the virgin proxies are not precisely fresh but were not used already for the particular websites that they are allocated in your package. This is why many sellers block access to sites other than the intended uses.
Used or resold Proxy
Although not explicitly mentioned, the majority of the proxies are previously used in one way or another. Since the websites remove the ban of a proxy after a particular time, using previously used proxies is perfectly fine after the time is over and the site supposedly lifts the ban.
Okay, Time to sleep and should end here!