Make no mistake about it; browser fingerprinting can be used to uniquely identify you and track you online. Come in now read our article on how to prevent browser fingerprinting.

Some people think all they have to do to prevent any tracking attempt is to route their web requests through proxy servers and prevent websites from storing cookies on their browsers and removing any information saved in HTML5 storage.
However, the truth of the matter is, websites have device other means to keep eyes on you, using a technique that is one of the most difficult techniques to prevent – browser fingerprinting. This article will discuss how to prevent Browser Fingerprinting. But before that, what is Browser Fingerprinting?
What is Browser Fingerprinting?
Browser Fingerprinting is the method of using one's browser settings and attributes to identify him online. It makes use of the principle that despite using the same browser, people’s browser attributes and settings, system properties, location information differs and can be used as a means of identification.
This means the more unique your browser settings and attributes are, the more unique your Browser Fingerprint. If you do not allow yourself to be tracked physically, why should you allow yourself to be stalked online?

There is a general consensus among standard bodies that Browser Fingerprinting is harmful. Despite this, the practice has gone on for decades, with players ranging from single sites to companies that track Internet users all over the Internet to state-level actions that are kept private for security reasons.
Being that as it may, Browser Fingerprinting is privacy intruding in nature. In most cases, you are not aware you are being tracked. Even when you are aware, preventing it can be difficult.
Why Fight Against Browser Fingerprinting Yourself

Browsers are supposed to be concerned about the privacy of their users and what sites actually do with the information they help them collect from users. When it comes to fingerprinting, not all browsers can be trusted in preventing Browser Fingerprinting.
Take, for instance, Google’s Chrome claim to make use of an anti-fingerprinting system to provide privacy for its users. However, because of its interest in the advertisement, it allows advertisers to still track users. This means while Chrome claim to be anti-fingerprinting, it can’t be trusted.
The truth is, if privacy is of major concern to you, you just have to be wary of all things, Google, as they strive to get data for their marketing campaigns. The better browser to use preventing Browser Fingerprinting is Firefox. Yes, Chrome won the browser war but cannot be trusted in terms of users’ privacy.

Solution
Even with the numerous browsers trying to prevent Browser Fingerprinting, you still need to go extra miles because some of them can evade the checks of the browsers. There are basically two ways to protect yourself from Browser Fingerprint – stopping websites from getting fingerprints of your browser or spoofing Browser Fingerprint.
How to block Browser Fingerprinting
Use Privacy-focused Browsers

Mainstream browsers like Chrome, Opera, and Firefox have one problem in common – they are not good at protecting your data when it comes to Browser Fingerprint. If you want to protect your browser against fingerprint, then you need to ditch that mainstream browser you are using. Privacy-focused browsers are the best for you. Two popular examples are Brave and TorButton.
They do not allow storing of data and clear cookies on their own after every session. TorButton is known for standardizing browser fingerprint by providing the same browser data for allusers. This makes the fingerprint to be one and as such, useless to the sites collecting them.
Recent development in Firefox is getting privacy concerned individuals to move towards Firefox. Firefox, through a third-party (Disconnect), keeps a list of sites that engage in Browser Fingerprinting and stop them from accessing information that will aid them in generating a fingerprint.
Disable JavaScript
The most effective way to block websites from getting browser information is to disable JavaScript on your browser. JavaScript is a front-end scripting language that can be used for making websites responsive and provide a better user experience. However, they are the main tool sites uses for getting Browser Fingerprinting information. If you disable JavaScript, there is no how a site will be able to create a fingerprint of your browser as only a few browser information such as User-Agent string name and a few other information will be available.
For Browser Fingerprinting, the more information available, the better the system will be at uniquely identifying your browser. However, having JavaScript disabled means you will not be able to access some sites that rely heavily on JavaScript. Some sites will still work without JavaScript, though.
Use Common hardware / browser

The whole idea of Browser Fingerprint makes a lot of sense only if devices can be differentiated. Instead of having the fear of websites getting fingerprint of your browser, you can avoid caring about it all together by making use of hardware and browsers that are common. Because you are using a common browser or hardware, you become less unique and as such, you can be grouped among the crowd.
Example of hardware to use is Macbook because a good number of people are using them, So you're less unique online!
How to Spoof Browser Fingerprint
Disabling Javascript means you won’t have a better web experience as some functionalities will be disabled. Instead of trying to compromise not using JavaSript, you can simply spoof and fake the information collected thereby making them useless.
Virtual machine

A Virtual Machine (VM) is a software-defined computer hosted on a server with its own operating system different from the underlying operating system. If you are using a VM, the Browser Fingerprint gotten will be that of the VM’s browser and not your real browsers Fingerprint. In this case, a VM gives out a unique Browser Fingerprint – but it is not for your own browser. Examples of VM includes Parallels Desktop, Oracle VM Virtualbox, and Microsoft Hyer-V, among others.
Use a User-Agent Spoofer
A client’s User-Agent string is one of the attributes used for profiling. If you are able to spoof and fake it, you are a step ahead to make the information collected inaccurate.
Chameleon is very effective for this. It comes with User-Agent strings for a good number of browsers. While you can make use of a static User-Agent, I will advise you go for the rotating ones that changes your User-Agent after a specified interval of time.
More, User-Agent Switcher to spoof your UA strings
Spoof your Canvas API
HTML5 Canvas originally meant for graphics has become one of the most powerful fingerinting tools because of the variations in how browsers treat them. You can prevent Canvas Fingerprint by using CanvasBlocker. This browser extension will block the Canvas API or fake your Canvas AP.
Use Multilogin – best browser spoofer for automation
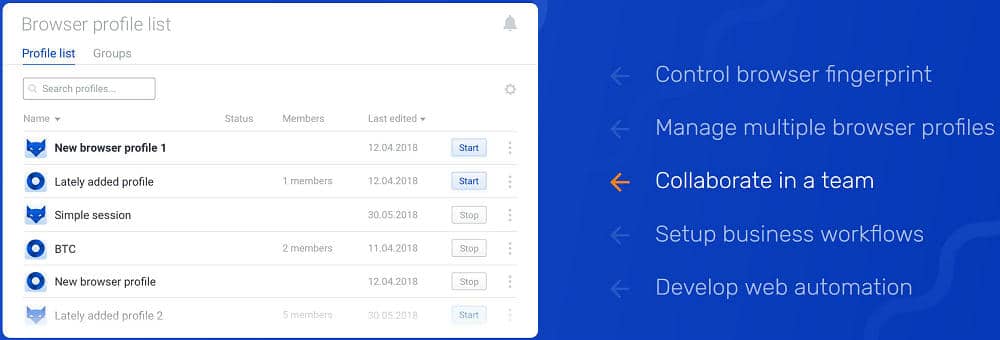
If you have got some budget, the best way to spoof your Browser Fingerprint is by using Multilogin. Multilogin is the ultimate tool for spoofing your browser attributes. It replaces multiple computers with virtual browser profiles, You can use it to create Facebook multiple accounts for FB Ads.
However, it requires monthly payment and that will keep some people away.
Related to Automation,
- The Best Facebook Proxies for FB Automation Bots
- The Ultimate Guide to Instagram Proxies for IG automation
- Best YouTube Bots to Get Free YouTube Views, Subscribers, Likes…
- Why Proxies are Key to Automation Bot
Conclusion
While there is a general consensus among standard bodies that Browser Fingerprinting can be harmful, there’s no sign that it is going to be stopped soon.
Browsers are already acting to prevent, but then, their solutions are not 100 percent foolproof. That’s why you need to apply other methods to prevent sites from generating a unique fingerprint of your browser.
Last, If you want to anonymity, You need to hide your IP address. you can use proxy server or VPN service to mask your IP address to protect your online identity.